So you want to use your own DNS server on your iPhone or iPad. Maybe your dns server is also a dnsbl (DNS Blocklist or DNS Blacklist) that you use to block unwanted ads, telemetry and malware. This might be something like Pi-Hole, PFBlockerNG, or void-zones-tools. Maybe you are even running void-zones-tools on OpenBSD as I describe in the HOWTO here.
Whatever your DNS server you want to use it, and you are having trouble because for some reason your iPhone doesn’t seem to be using your DNS server. Even though your DHCP server hands out the right DNS to the phone it still seems to bypass it. You see your DNS server listed properly in the Wi-Fi configuration in the iPhone, but nevertheless it is no being used. You are still seeing ads, and resolving sites you shouldn’t be.
It seems at some point Apple decided to helpfully forward DNS through iCloud. Have a look at Setting->Wi-Fi and tap the little blue letter I in the circle next to your Wi-Fi network. Scroll down under DNS and tap on Configure DNS. This brings you to the following screen:
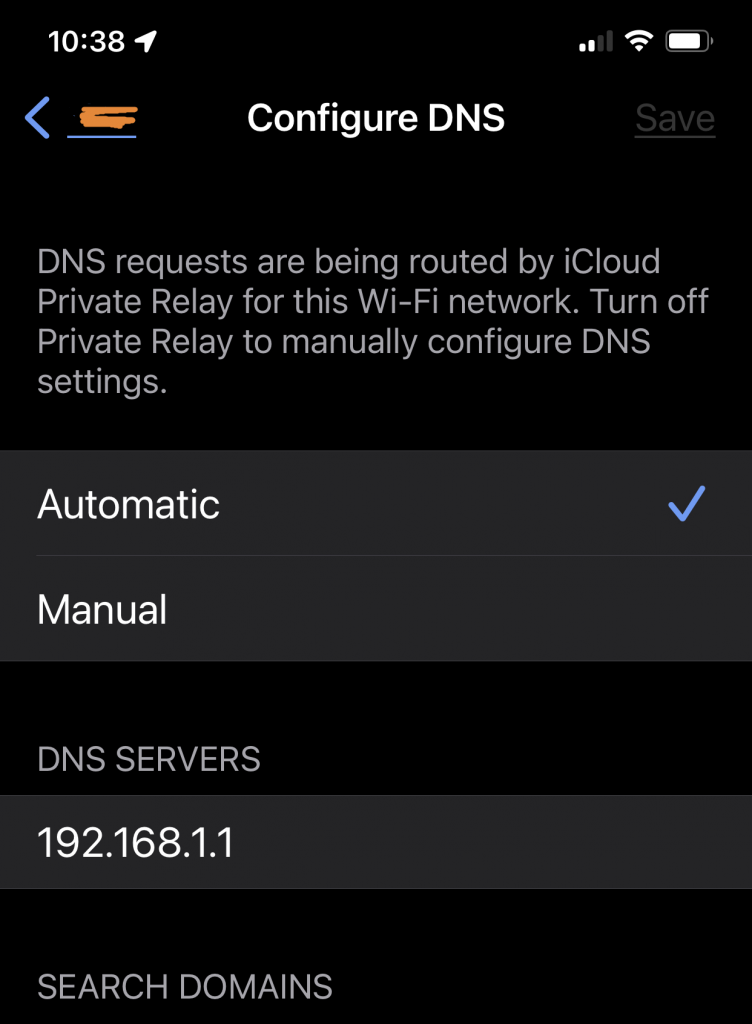
Note that it has a warning that:
“DNS requests are being routed by iCloud Private Relay for this Wi-Fi network. Turn off Private Relay to manually configure DNS settings.”
The annoying this that Private Relay is indeed turned OFF. So this phone is still routing DNS through iCloud even though Private Relay is turned off. We need to bypass Private Relay for DNS. Luckily there is a way!
Apple has a document describing Private Relay here. The specific part we are concerned with is here:
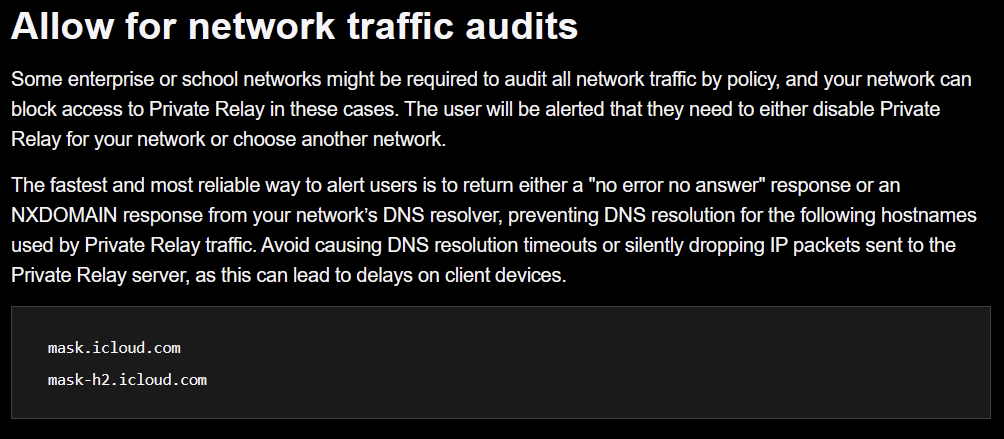
This same technique can be used to prevent DNS being routed through iCloud even when Private Relay is turned off. We just need to use our trusty DNS server to return NXDOMAIN for those offending addresses and Apple will butt out of our DNS!
(Note that I am fairly certain this will also disable Private Relay completely. So if you actually need Private Relay and don’t have your own VPN this may not be the best solution for you. But if you are running your own DNS server chances are you at least somewhat know what you are doing and can cogently evaluate this on your own.)
How you fix this is dependent upon which DNS server you use.
In order to fix this under pfBlockerNG (a dnsbl that runs on pfSense):
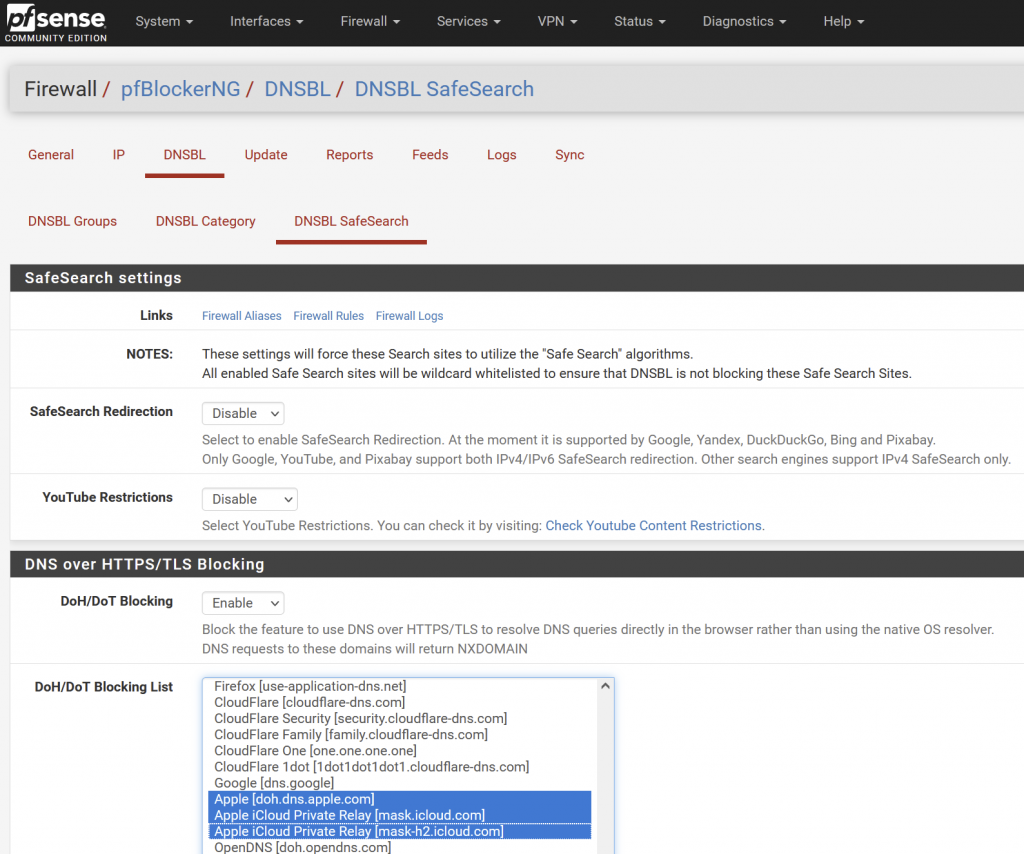
Be sure to Enable DoH/DoT Blocking and then select the Apple servers as shown. Note the additional server doh.dns.apple.com I believe will block HTTPS dns requests on the Mac from going to Apple and force those to use your local server instead. Enable if you wish, though it is not required to fix the issue.
To fix this with void-zones-tools:
Edit your /usr/local/etc/void-zones/my_void_hosts.txt file and add the following entires under #blac klist:
#black list
0.0.0.0 mask.icloud.com
0.0.0.0 mask-h2.icloud.comRe-run void-zones-tools.sh and restart unbound. (If you are running void-zones-tools I assume you know how to do these things. If you have forgotten check your crontab, because you would have set them up in there to keep the lists up to date.)
To fix this under Pi-Hole:
(Note I do not run Pi-Hole. This info is taken from the following link. YMMV)
Create a file /etc/dnsmasq.d/xx-NXDOMAIN.conf , (replace xx with an unused number). Put the following lines in that new file:
server=/mask.icloud.com/
server=/mask-h2.icloud.com/
Then restart pihole-FTL (sudo service pihole-FTL restart).
To fix this with any other DNS server:
Just configure your server to reply with an NXDOMAIN for those two addresses:
mask.icloud.com
mask-h2.icloud.comWhen the iPhone / iPad see this it will use your own DNS server, bypassing iCloud Private Relay for DNS.
Conclusion
Apple has made the unilateral decision to slurp up everybody’s DNS queries in the name of security. (Granted, they do handle it a pretty decent way, as opposed to say, Google’s 8.8.8.8, etc.) Most nerds want to use their own DNS servers for a myriad of reasons. This articles describes how to make IOS use your own DNS on an iPad or iPhone by disabling Private Relay for DNS.